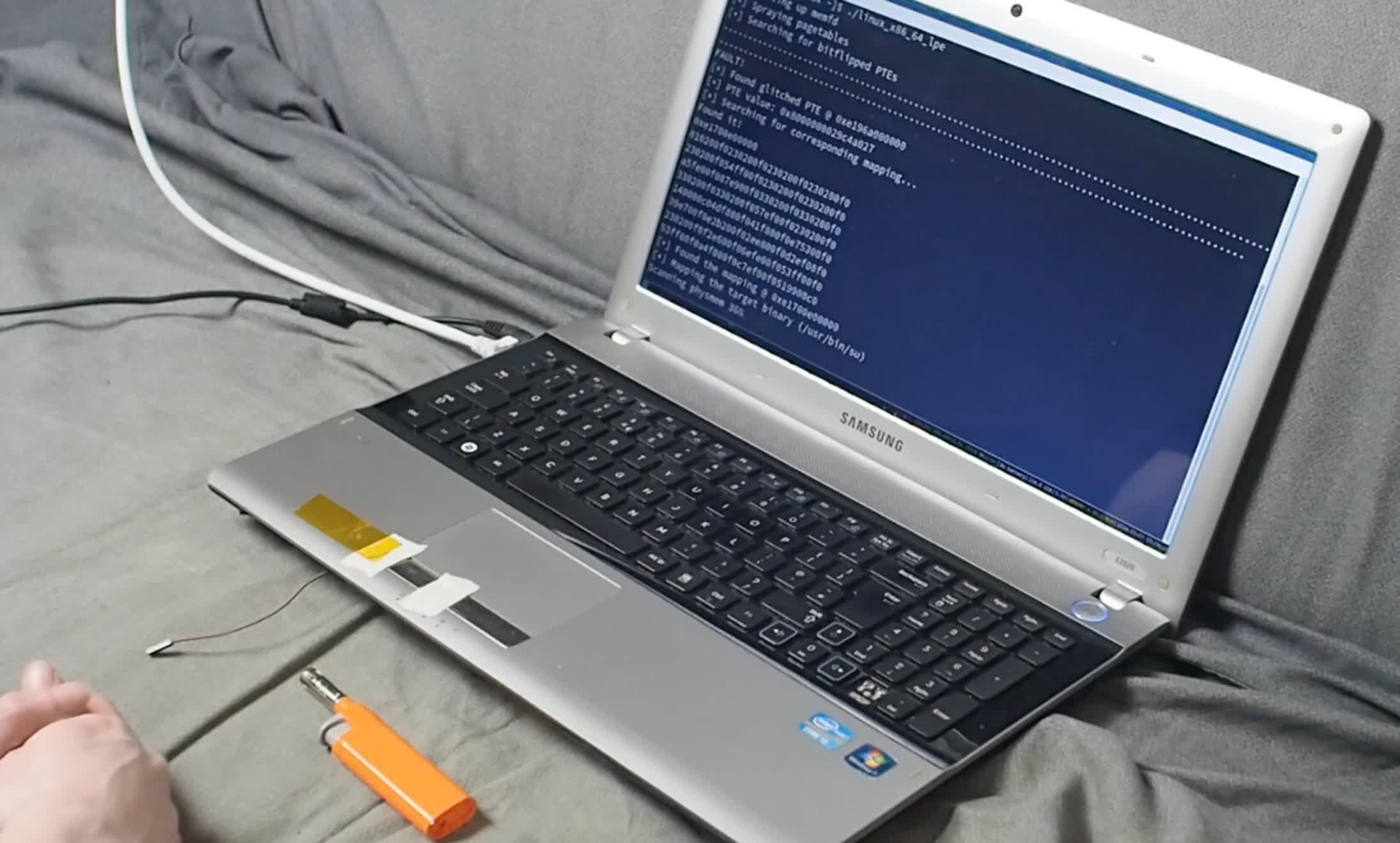
Buchanan walks through his process of experimenting with low-cost fault-injection attacks as an alternative when typical software bugs aren't available to exploit.
Not if the storage is encrypted. That's why vulnerabilities in operating systems/kernel are so impactful, as they can bypass that encryption.
It's a bit more nuanced even.
If you have one-time physical access, then you have total access, permitting the storage is not encrypted.
If you have recurring, undetected physical access, then you have total access.
Ex: Dropping a script into someone's unencrypted /boot partition that captures the decryption credential, then coming back later to collect the credential and maybe also remove the evidence.
That is impressive. However, if you have physical access to the RAM, you can probably also just pop in a live USB, chroot into the system and do whatever you want. Regardless, this injection was interesting and impressive. Hats off to a clever hacker like that.
Yeah, it's wild to me that desktop operating systems don't encrypt storage by default. Both iOS and Android do.
The threat profile for a desktop is different than a phone.
You carry your phone with you everywhere.
Desktops typically stay in one location that likely has locks.
If you're truly paranoid, you'll encrypt your drive regardless. For regular joes like me, it's not enough for me to enable it and enter a password at boot up.
The modder in the article mentioned that the method could be used to break copyright protections on game consoles, can someone explain that?
I assume this doesn't apply to consoles or harware that verify keys over the network, since the decryption key isn't stored on the device itself? This is more for things like Blu-ray players or consoles that read physical media, right?
I'm a hobbyist so sorry if that's a dumb question